All Windows PCs come with a built-in security feature called Windows Defender Application Control (WDAC), which helps prevent unauthorized software from running by allowing only trusted applications.
However, despite its purpose, hackers have discovered several ways to bypass WDAC, exposing systems to malware, ransomware and other cyber threats.
As a result, what was once considered a strong layer of defense may now serve as a potential vulnerability if not properly managed.
STAY PROTECTED & INFORMED! GET SECURITY ALERTS & EXPERT TECH TIPS — SIGN UP FOR KURT’S THE CYBERGUY REPORT NOW
Image of a Windows laptop. (Kurt “CyberGuy” Knutsson)
What is Windows Defender Application Control (WDAC) bypass?
Windows Defender Application Control (WDAC) is a security feature in Windows that enforces strict rules about which applications can run. It helps block unauthorized software, but researchers have found ways to bypass these protections.
Bobby Cooke, a red team operator at IBM X-Force Red, confirmed that Microsoft Teams could be used as a WDAC bypass. He explained that during Red Team Operations, they were able to get around WDAC and execute their Stage 2 Command and Control payload.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
To find and fix these security gaps, Microsoft runs a bug bounty program that rewards researchers for reporting vulnerabilities in WDAC and other security components. However, some bypass techniques go unpatched for long periods.
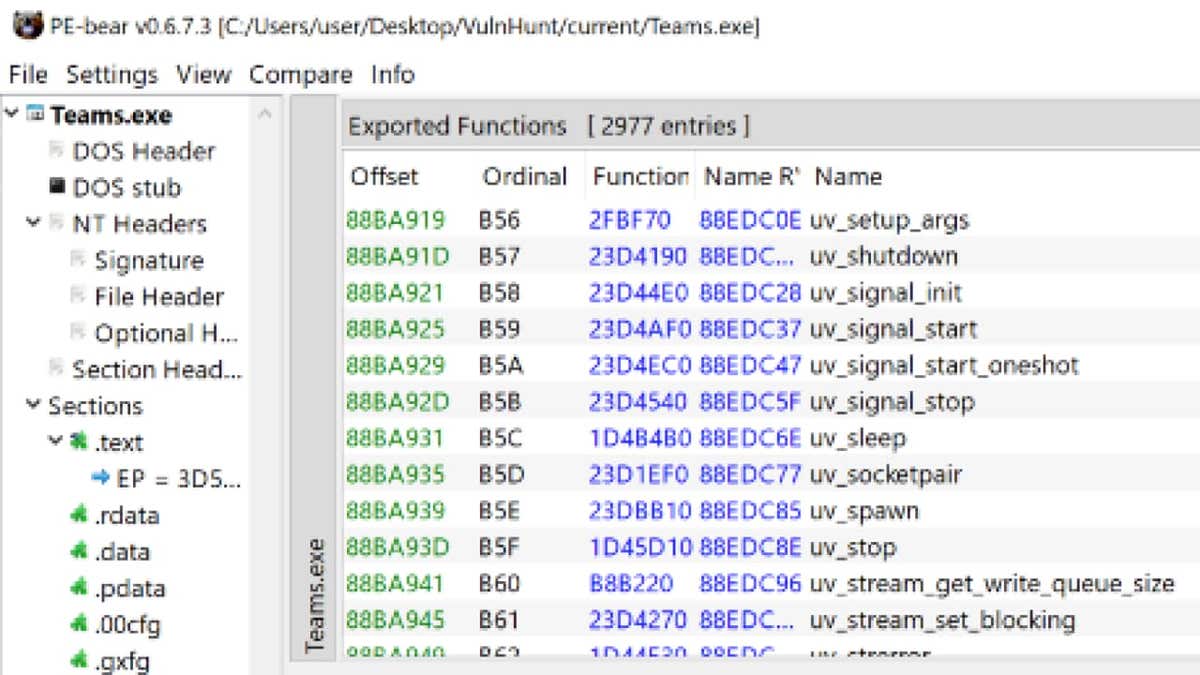
Teams Electron API Surface revealed. (IBM)
DOUBLECLICKJACKING HACK TURNS DOUBLE-CLICKS INTO ACCOUNT TAKEOVERS
How hackers bypass Windows Defender Application Control
One of the key ways attackers get around WDAC is by using Living-off-the-Land Binaries, or LOLBins. These are legitimate system tools that come pre-installed with Windows, but hackers can repurpose them to execute unauthorized code while avoiding security detection. Since these tools are trusted by the system, they provide an easy way to slip past defenses.
Some bypass techniques involve DLL sideloading, where attackers trick legitimate applications into loading malicious DLLs instead of the intended ones. Additionally, if WDAC policies are not enforced properly, attackers can modify execution rules to allow unauthorized software to run.
Hackers also use unsigned or loosely signed binaries. WDAC relies on code signing to verify an application’s authenticity. However, attackers sometimes exploit misconfigurations where loosely signed or unsigned binaries are mistakenly allowed, letting them execute malicious payloads.
Once an attacker bypasses WDAC, they can execute payloads without being flagged by traditional security solutions. This means they can deploy ransomware, install backdoors, or move laterally within a network without triggering immediate suspicion. Since many of these attacks use built-in Windows tools, detecting malicious activity becomes even more difficult.
WINDOWS DEFENDER VS ANTIVIRUS SOFTWARE: FREE PROTECTION FALLS SHORT

Image of a Windows laptop. (Kurt “CyberGuy” Knutsson)
RELENTLESS HACKERS ABANDON WINDOWS TO TARGET YOUR APPLE ID
3 ways you can protect your PC from WDAC hackers
Since this attack exploits a vulnerability within WDAC, there is little you can do to fully protect yourself. It is up to Microsoft to fix the issue. However, here are three best practices you can follow to reduce your risk.
1. Keep Windows updated: Microsoft regularly releases security updates that patch vulnerabilities, including those related to WDAC. Keeping Windows and Microsoft Defender up to date ensures you have the latest protection against known threats. If you’re not sure how to do that, see my guide on how to keep all your devices and apps updated.
2. Be cautious with software downloads: Only install applications from trusted sources like the Microsoft Store or official vendor websites. Avoid pirated software, as it can come bundled with malicious code that bypasses security protections like WDAC.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?
3. Use strong antivirus software: Based on the report, it does not appear that hackers require user interaction to bypass WDAC. The methods described suggest that an attacker could exploit these vulnerabilities without direct user input, especially if they already have some level of access to the system.
However, in real-world scenarios, attackers often combine such exploits with social engineering or phishing to gain initial access. For example, if an attacker gains access through a phishing attack, they might then use WDAC bypass methods to execute further malicious payloads.
So, while direct user input may not be necessary for some bypass techniques, attackers often use user actions as an entry point before exploiting WDAC vulnerabilities. The best way to avoid becoming a victim is to have a strong antivirus software installed. Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices.
CLICKFIX MALWARE TRICKS YOU INTO INFECTING YOUR OWN WINDOWS PC
Kurt’s key takeaways
While Windows Defender Application Control (WDAC) offers a valuable layer of security, it isn’t foolproof. Hackers are actively developing and using WDAC bypass techniques to exploit gaps in system defenses. Understanding how WDAC bypass works is essential to protecting your devices. By keeping your software up to date, using trusted applications, and relying on reputable security tools, you can significantly lower your risk.
CLICK HERE TO GET THE FOX NEWS APP
Do you think Microsoft is doing enough to patch these vulnerabilities, or should it take stronger action? Let us know by writing us at Cyberguy.com/Contact
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most-asked CyberGuy questions:
New from Kurt:
Copyright 2025 CyberGuy.com. All rights reserved.

